What Is Terraform And Why Is It Needed?
Infrastructure as a Code Using Terraform

Image from Hashicorp Learn

The Traditional Approach
When getting started in the cloud, users most often create their cloud infrastructure using a management console. The management console provides a user friendly graphical display that allows for pointing and clicking to create resources. For a small organization in a single region, the management console can be a practical solution. The problem begins with the need to replicate the resources in new regions or accounts.
Imagine creating a complex environment manually using the management console, then having to create similar environments for another region or account. Everything would need to be manually replicated. Now imagine even more requests to create similar environments. To make matters worse, there needs to be a change to one of the resources that impacts each environment, so each environment will need to manually modified through the console.
Easily this could begin to spiral out of control and prevent the developer from getting anything accomplished besides manually building and maintaining cloud infrastructure. Not only an inefficient use of time to create and maintain everything, but it’s also error-prone.
Infrastructure as Code
Infrastructure as Code (IaC) can be thought of as a scalable blueprint for an organization’s environment that gains the ability to use the same tools as developers such as version control, testing, code reviews, and CI/CD. It allows developers to provision and configure environments in a reliable and safe manner. Rather than using the management console to manually create resources for multiple environments, a developer could use the existing IaC from the first environment to create the others, saving time, saving money and preventing errors.

Infrastructure in a code format grants visibility not present through infrastructure created manually. Developers have the ability to reference all the resources and parameters without having to use the console, making it easy to track and manage resources. Once the initial template has been created, it can be reused many times in multiple Regions for multiple Accounts. With a proper branching strategy using Git, IaC allows for version control and even the ability to roll back to a previous version if needed. A template following best security practices provides the assurance that all environments created from the template are following the same procedures and guidance.
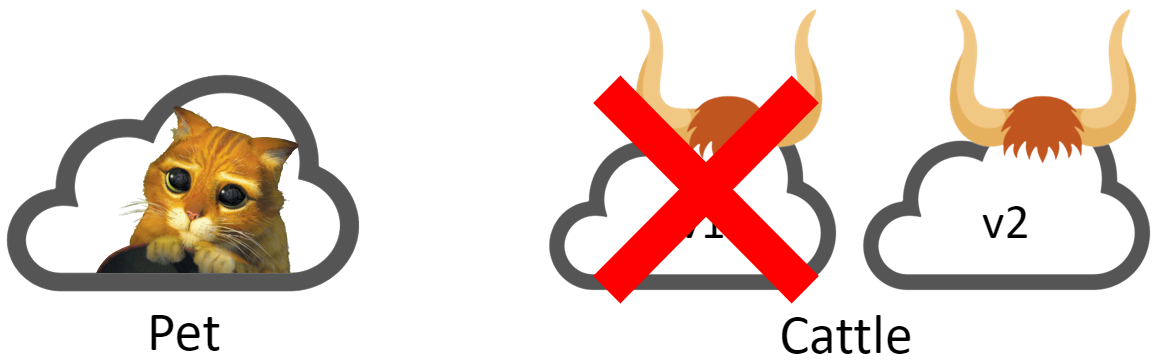
The introduction of the cloud challenged the traditional thought process of treating servers and other resources as pets to instead treat them as cattle.
Now Developers have the ability to rapidly create infrastructure and just as quickly tear it down. IaC makes this even more practical with the ability to create and destroy environments as necessary, preventing the need to keep resources running and rack up costs. By keeping the Iac file updated, the developer can ensure that when they need to spin up an environment, they will have everything they need.
All the major cloud providers have their own IaC offering with the drawback of only being able to be used for that specific cloud provider. A multi-cloud organization would require learning and using multiple services to accomplish the same task.

Photo by JESHOOTS.COM on Unsplash

Terraform
A cloud agnostic offering, HashiCorp’s Terraform supports both multi-cloud and on premises. It’s an open-source tool with an Enterprise version that uses HashiCorp’s own HashiCorp Configuration Language (HCL). Terraform’s HCL allows a developer to learn one language to work with multiple cloud offerings and on premises providers rather than having to learn a new service and language for each. HCL is a declarative language, focusing on the end state as opposed to a procedural language, where all commands are executed in the order written. Hashicorp provides documentation on Terraform for developers and their Terraform Registry can be accessed for both official and community templates. Terraform has the ability to import existing resources to be tracked through code if they were created outside Terraform. Terraform supports over 170 Official and Verified Providers to include AWS, Azure, Google Cloud, Oracle Cloud, Alibaba Cloud, Kubernetes, VMware, Docker, Databricks, GitHub, Gitlab, Splunk and Grafana to name a few.
Desired State
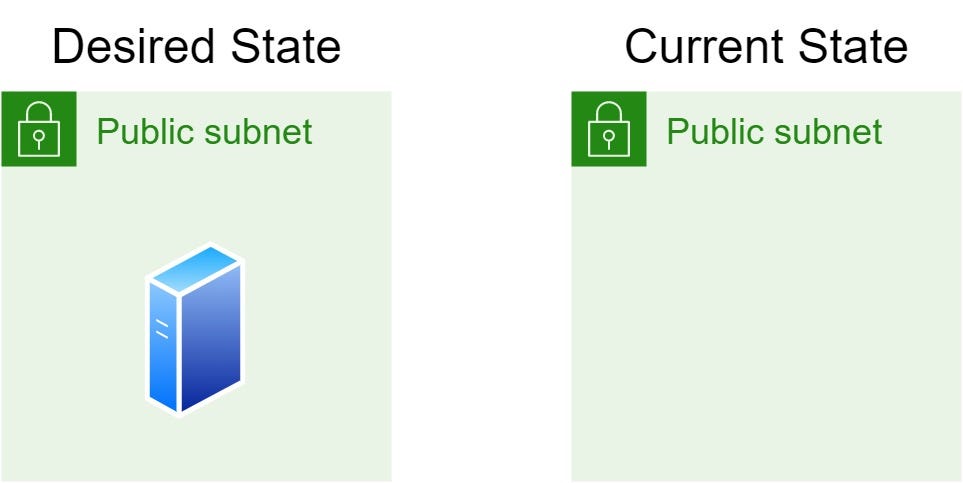
With Terraform a developer has the ability to map to existing resource configurations using the Terraform State File, which stores the state of your infrastructure. The State File tracks the desired state of your infrastructure and compares it to the current state of your infrastructure. As an example if the current environment doesn’t have any virtual servers and the Terraform file creates one virtual server, then when ran, Terraform will create one virtual server in your environment.
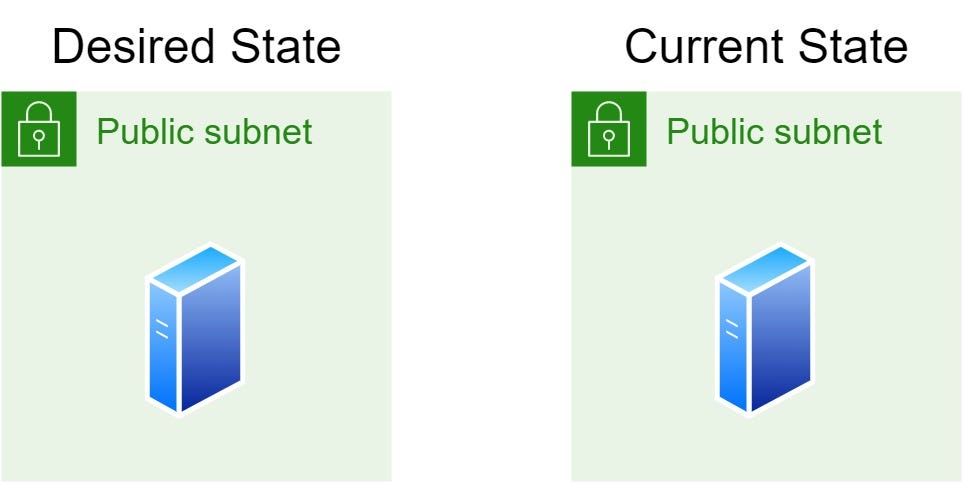
If run again with making any changes, the Desired State would match the Current State and no action would be taken.
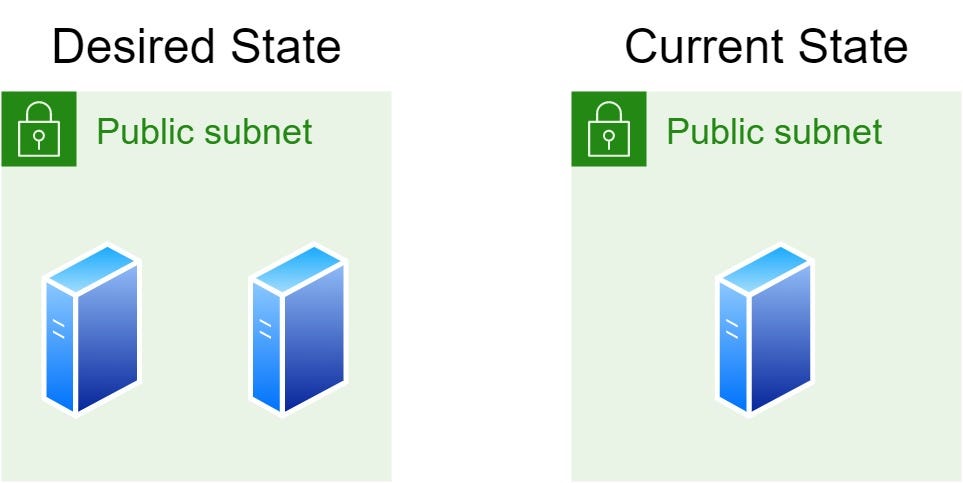
If the user was to update the Terraform file again to create two virtual servers and then run the Terraform file, Terraform would see that now the Desired State and Current State no longer match and add one virtual server.

Terraform Workflow
Each Terraform project will follow the Terraform Workflow consisting of 1) Write, 2) Plan, and 3) Apply.
1) Write
Write the IaC in HCL using blocks, arguments, variables, and expressions.
2) Plan
Run terraform plan to get a preview of the modifications that will be made to the environment. The plan output will notate what will be added, destroyed, and changed.
3) Apply
If satisfied with the plan output, run terraform apply to apply the desired changes to reach your desired state.
Terraform apply output

Tearing Down Environments
To remove a resource from the desired state of your environment, remove the resource from the Terraform file. Once removed Terraform will note that your desired state no longer includes the resource and will remove it from your environment. If ready to tear down the environment completely run the terraform destroy command to destroy the environment.
Terraform helps make Infrastructure as Code for an organization’s cloud environment simple and repeatable. For more information on Terraform, please visit Introduction To Terraform. For tutorials from HashiCorp visit Terraform Tutorials.
Check out Troy’s original post here – What Is Terraform And Why Is It Needed?
